pxGrid Context-In
pxGrid Context-in allows ecosystem partners to publish topic information into Cisco ISE allowing Cisco ISE to take action based on the identified asset. For more information on the Endpoint Asset Topic, please visit Endpoint Asset Topic
The ecosystem partner publishes the topic attributes to the endpoint asset topic. Cisco ISE will subscribe to this endpoint asset topic and consume this information. ISE profiling policies will be defined based on the published IOT diectionary attributes or customized attributes. This profiling policy will be assigned to the ISE authorization policy defining network access for classified devices.
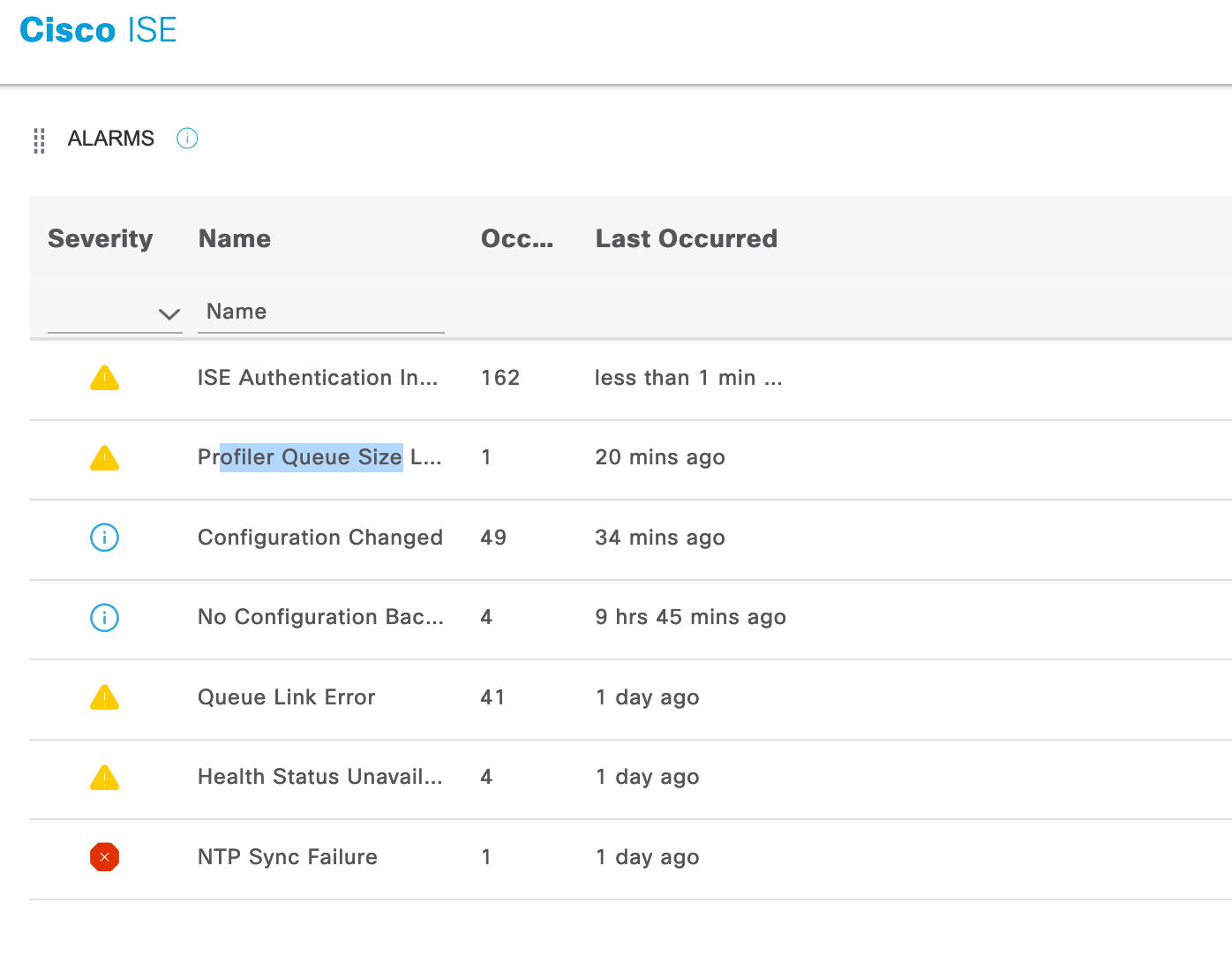
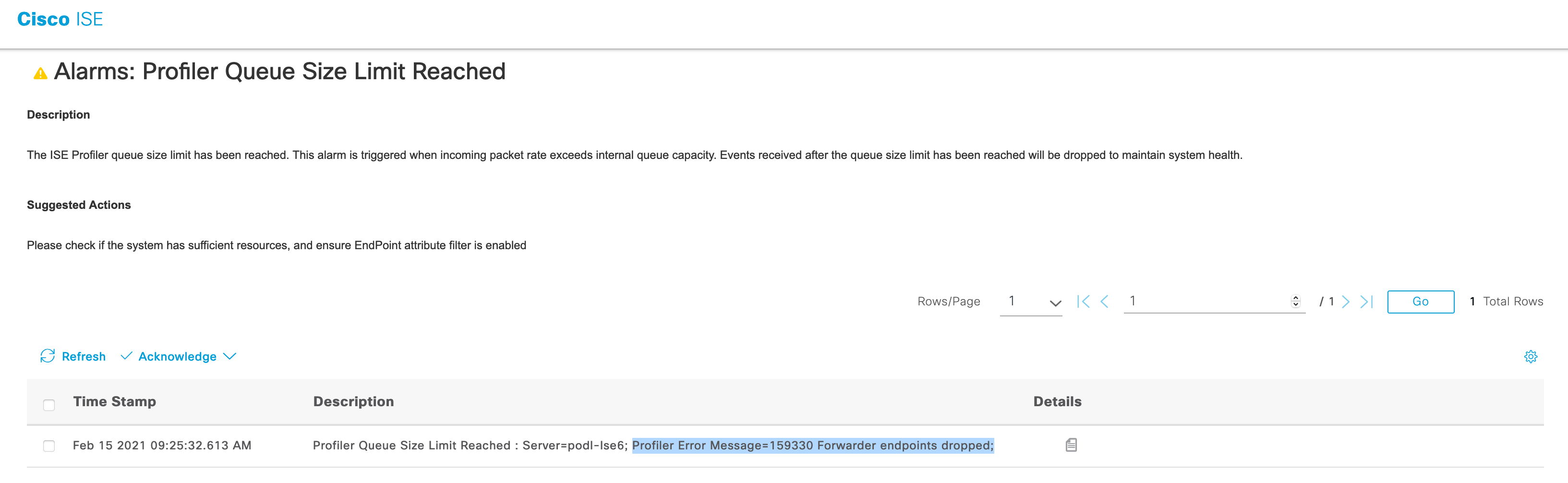
Note: pxGrid Context-in allows up to 100 transactions per second with the number of custom attributes as 10. Further increase in the traffic rate may cause unwanted issues, such as packet drops, but you will not see any errors in the transaction. The screenshots below show the alarms seen on Cisco ISE. As this function is tied to profiling, you will see the following alarms.
The example below represents an Internet of Things (IOT) Solutions Vendor, to see an example of a Security Solution publishing Threat Information into ISE, please see pxGrid Context-In Threat Example
Before accessing the pxGridContextIn code, please perform the following steps:
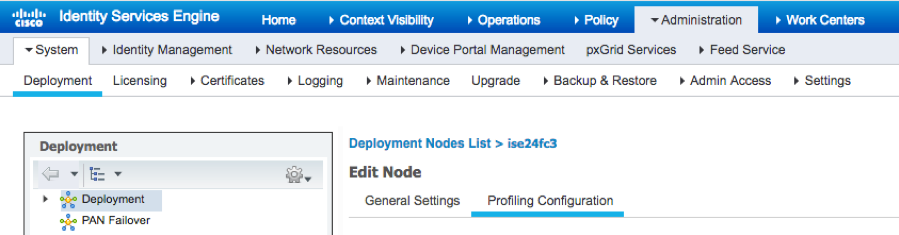
Enable pxGrid under Profiling Configuration
Select Administration->System->Deployment, edit the ISE node, and enable pxGrid under Profiling Configuration
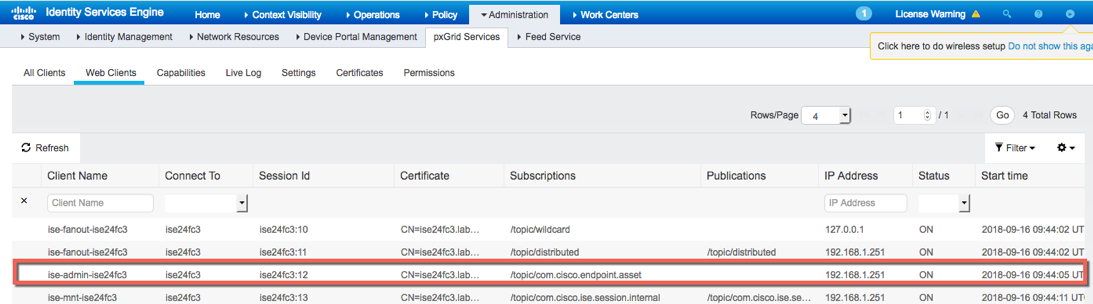
Verify that the ISE pxGrid node has subscribed to the endpoint asset topic Select Administration->pxGrid Services->Web Clients, you should see that ISE has subscribed to the endpoint asset topic
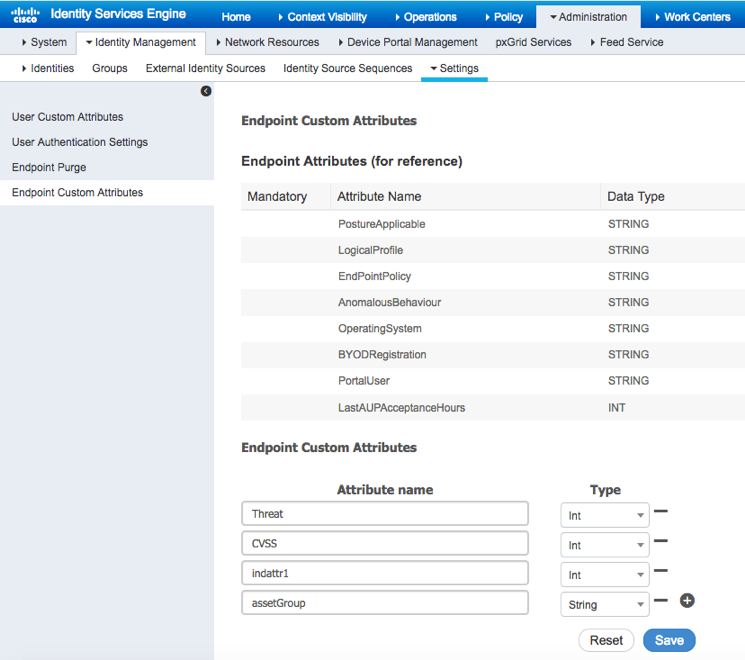
Define custom attributes (optional)
Define custom attributes Select Administration->Identity Management->Settings->Endpoint Custom Attributes and define the custom attributes. These attributes will also be defined in the pxGrid Context-In.java code.
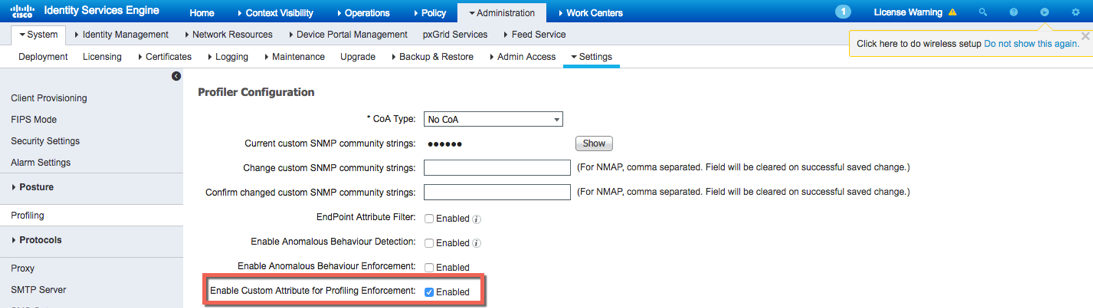
Enable custom attribute enforcement
enable custom attribute for enforcement Select Administration->System->Settings->enable Enable Custom Attribute for Profiling Enforcement
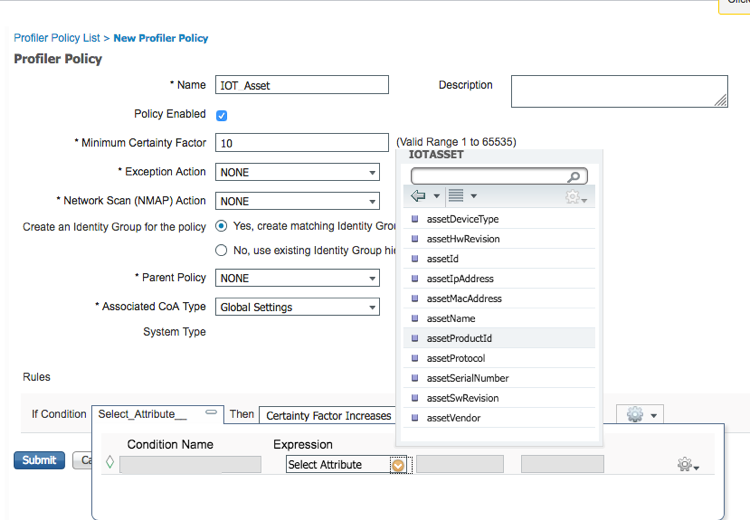
Define Profiling Policy based on IOT assets dictionary
IOT Asset Attributes Policy IOT Device Select Policy->Profiling->Profiling Policies->Add, enter the name of the profiling policy Under Rules->Select Attribute..->Create New Condition->Under expression->select new attribute->Dictionaries->IOT Assets You should see the following available attributes. These attributes are defined in the endpoint asset schema. The key values such as “assetId” and the attribute will be defined in the pxGridcontent-in.java app.
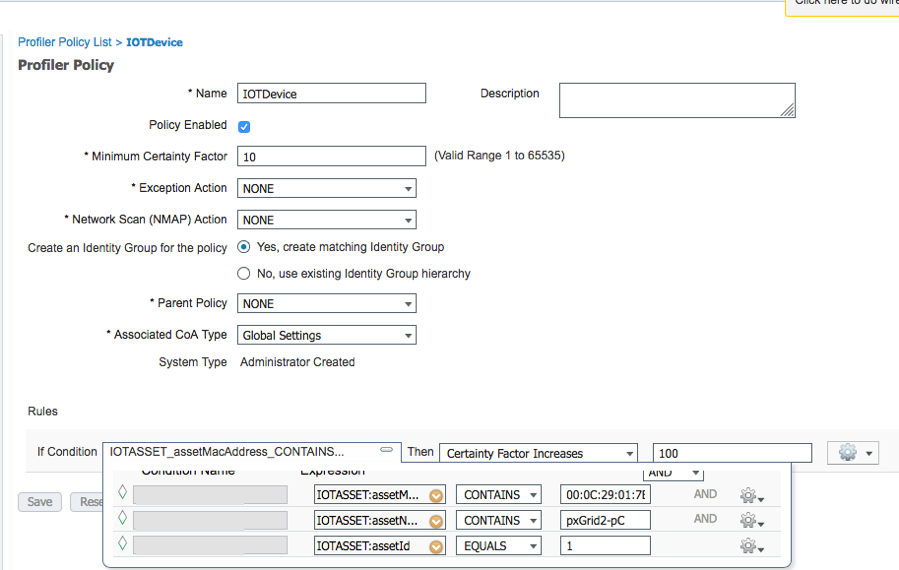
Select Submit In the example below, the IOTDevice profiling policy is defined. The IOTASSET:AssetMacAddress, AssetName, and AssetID are defined.
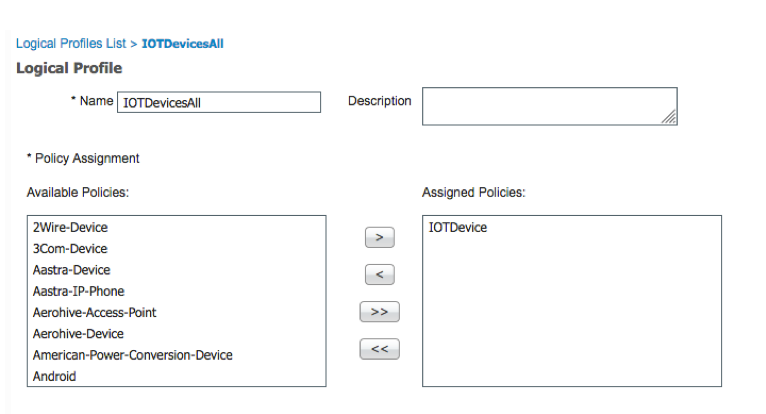
Define Logical Profile
Logical Profiles Select Policy->Profiling->Logical Profiles->Add enter the name of the logical profile name and assign selected policy(s) to it. i.e. IOTDevice
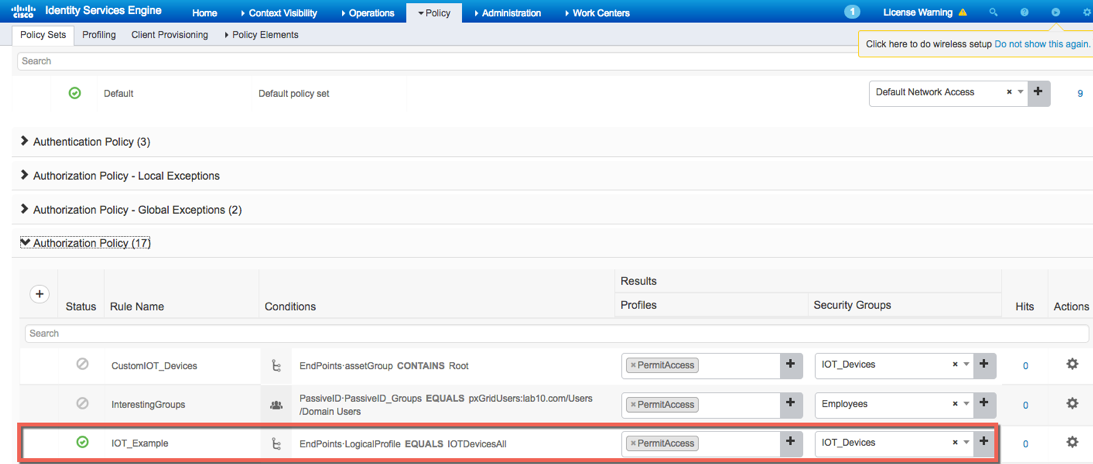
Define IOT Asset Policy
Select Policy->Policy Sets->View->click “>” Click on Authorization Policy Under Actions click on the gear and Insert new rule above For Rule Name, type IOT_EXAMPLE Click on Conditions, under Editor, under Dictionary select Endpoints->Logical Profile->Equals->IOTDevicesAll->Use Under Profiles select permit access Under Security Groups define IOT_Devices add to Security Groups. Select Save